WARNING: The “Tire Faster” and “Quality Garage Doors” Phishing Scam Targeting Web Agencies
If your web development, SEO, or digital marketing agency has recently received an inquiry from companies like Tire Faster or Quality Garage Doors, you need to read this immediately.
At first glance, it looks like a dream lead: a legitimate-sounding business reaching out with a massive budget for a straightforward website build. But beneath the surface lies a highly coordinated, sophisticated phishing scam designed to completely compromise your agency’s Google Workspace and, ultimately, your clients’ websites.
These two domains—along with a rotating cast of hijacked or spoofed business identities—are currently being used in a targeted OAuth Consent Phishing attack. Here is exactly how the scam works, the red flags to watch out for, and how to protect your agency.
How the Scam Operates
The threat actors behind this campaign have done their homework. They understand the sales processes of digital agencies and have crafted a trap that exploits standard onboarding procedures.
Phase 1: The “Too Good to Be True” Lead
The scammers reach out via email or your website’s contact form. They pose as representatives of real businesses (often using names like “Oliver Willson” for Tire Faster or “Daniel Miller” for Quality Garage Doors).
They will present a highly lucrative budget—often $50,000 or more for a basic 7-to-10-page website. To make the request look authentic, they will provide a highly detailed, multi-page PDF outlining their technical specifications and project requirements.
However, they will aggressively avoid getting on a phone call or Zoom meeting, insisting that they are “too busy” or “traveling,” and demand to keep all communication strictly to email.
Phase 2: The Fake Staging Environment
Once they have your attention, they will claim they use a unique, highly secure hosting setup (often name-dropping popular hosts like WP Engine). They will ask you to review their current backend or staging site to assess the project.
They will provide a link that looks something like: http://wpengine.dev-tirefaster.com/dev-admin
Phase 3: The Payload (OAuth Phishing)
When you click the link, you aren’t taken to a WordPress login screen. Instead, you are redirected to what appears to be a standard Google Authorization portal. The “client” will instruct you to complete this “Google Authorization” to gain access to their secure server.
This is the trap. If you click “Allow,” you are not logging into a staging site. You are unknowingly granting a malicious third-party application a long-lived “Refresh Token” to your Google account.
Why This Attack is So Devastating
Unlike traditional phishing that tries to steal your password, an OAuth phishing attack is far more dangerous because it bypasses Two-Factor Authentication (2FA). By clicking “Allow,” you hand the scammers a skeleton key to your Google account. Once inside, they typically execute a devastating playbook:
-
Hidden Access: They set up invisible email forwarding and deletion rules so you never see security alerts from Google.
-
Data Scraping: They scan your Gmail, Google Drive, and Google Search Console for passwords, FTP credentials, and WordPress logins belonging to your actual clients.
-
The Ripple Effect: They use your stolen credentials to log into your clients’ websites, injecting malware, redirect spam, or Black Hat SEO links.
Red Flags to Watch Out For
To protect your agency, train your sales and technical teams to spot these warning signs:
-
Massive budgets for simple work: If someone is offering $50k+ for a basic brochure website, be skeptical.
-
Refusal to meet: Legitimate clients dropping five figures on a website will want to speak with you via phone or video.
-
Lookalike email domains: The scammers often email from domains that are slightly off, such as
@qualitygaragedoorsca.us.cominstead of the actual company domain. -
“Google Authorization” for WordPress: You should never need to grant a third-party app access to your Google account to view a client’s WordPress staging environment.
What to Do If You’ve Been Targeted
If you are currently talking to them: Cease all communication immediately. Do not click any links, and run a malware scan on your computer if you downloaded their project brief PDFs.
If you clicked the authorization link: You need to act immediately to lock them out. Changing your password is not enough because the OAuth token bypasses passwords.
-
Go to your Google Account settings (Manage Your Google Account).
-
Navigate to Security > Third-party apps with account access.
-
Review the list of apps. If you see anything you do not explicitly recognize (especially apps vaguely named “WP Engine Auth” or “Staging Access”), revoke its access immediately.
-
Check your Gmail settings for any hidden forwarding rules or filters you didn’t create.
-
Audit your client websites for unauthorized admin users or recently modified core files.
Share this warning. These scammers rely on agencies operating in silos. By sharing this information with your network, you can help shut down their lucrative pipeline and protect the web development community.
*** Have you encountered this scam or one similar to it? Let us know in the comments below so we can keep the community updated on the latest tactics.
Like Our Content? - Want To Discuss Your Business?
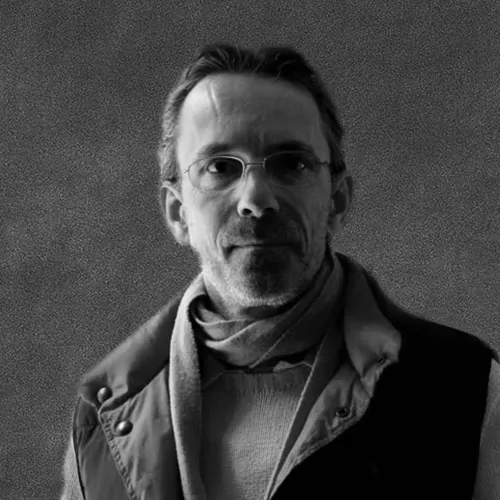
Digital Artist and Marketer | Business Consultant & Advisor.
Hans van Putten owner of 40parkLane,llc ran operations of his food manufacturing company for 17+ years building the Carolyn’s Handmade brand under the umbrella of 40ParkLane,llc.
After the successful sale of the food business, he took advantage of the years of business planning, operations management, web design, digital marketing and photography experience , to help startups, small businesses and home businesses and has been involved in a number of start-up ventures since.
Prior to founding 40parkLane,llc Hans worked for the Gillette Company for 10 years in various financial roles of increasingly bigger responsibility, leaving as Director of Business Planning for The International Group at Gillette HQ, Boston. Hans has an MBA (Marketing & International Business) from Aston University, and a BA in Business Administration from IHBO de Maere.